Alias Robotics leads the Cyber Security for Robotics Workshop (CS4R) at ERF2020
Alias Robotics continues showing leadership in the global robot cyber security landscape by leading the Cyber Security for Robotics Workshop (CS4R) at the European Robotics Forum 2020 #ERF2020.

Alias Robotics consolidates leadership in the global robot cybersecurity landscape. In this case, our team led the Cyber Security for Robotics Workshop (CS4R) at the European Robotics Forum 2020 #ERF2020 in Málaga (Spain).
If you're interested in the workshop's content visit their sites at:
A full room of Roboticists
The attendance to the workshop was first class. We had an almost packed room with an audience that launched quite a few questions throughout the workshop. Lots of interest in robot cybersecurity field emerged in the last couple of years and has clearly confirmed in ERF2020.
Best-in-class invited speakers together with the audience discussed their views on cybersecurity in robotics with paticular focus in the Challenges of the European community.

Highlights of the robot cybersecurity workshop
Let's summarize some of the key conclusions and highlights of the robot cybersecurity workshop:
Releasing Alurity EDU
Alias Robotics presented updates on cybersecurity tools and made available to researchers and students alurity EDU, an initiative that will provide students and researchers with free access to Alurity meant for Universities, higher education schools and research centers.
Alurity is a toolbox for robot cybersecurity. A modular and composable toolset featuring dozens of different tools that simplifies system integration and speeds up the cybersecurity research in robotics. As simple as building your virtual robotics set up and challenging it.

"Alurity ensures that security researchers working in a project, have a common, consistent and easily reproducible development environment which greatly facilitates the security process (exploitation and mitigation) and the collaboration across teams. It is now available for Linux (across distributions) and soon will be available in Mac OS and Windows" shared Víctor Mayoral Vilches, CTO at Alias.
A panel discussion was held with the speakers, including an Interactive Q&A session.
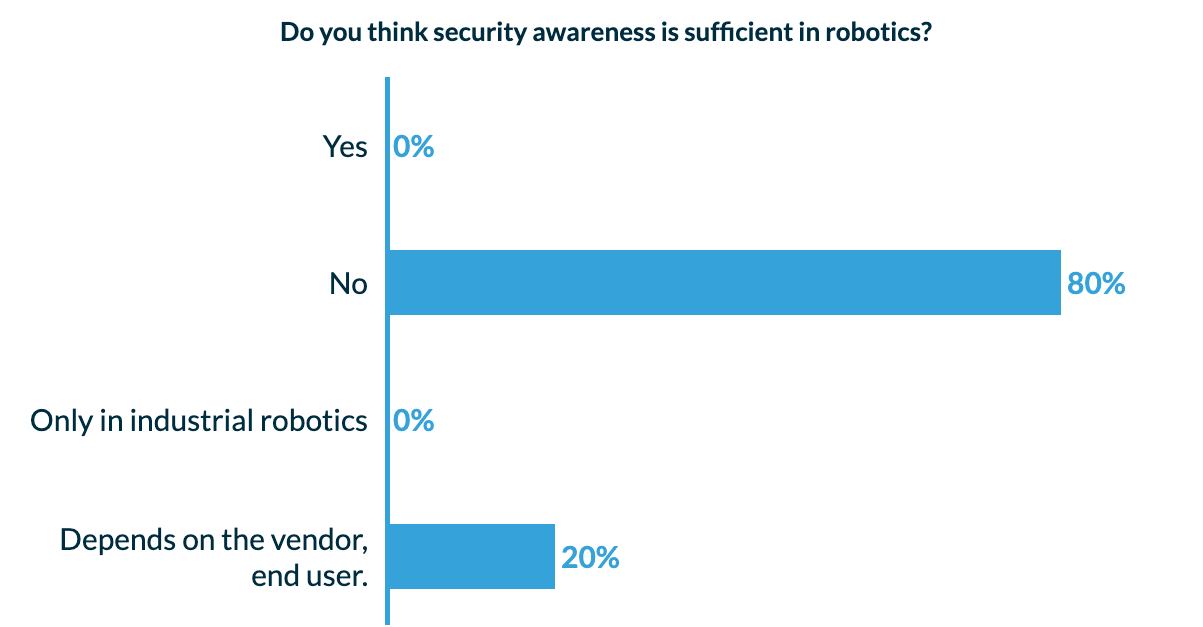
Security awareness is not sufficient in robotics
80% of the audience judges security awareness not to be sufficient in robotics while a 20% considered that it depended on the vendor. The big picture depicts some actions to be taken, surely, and lessons to be learnt.
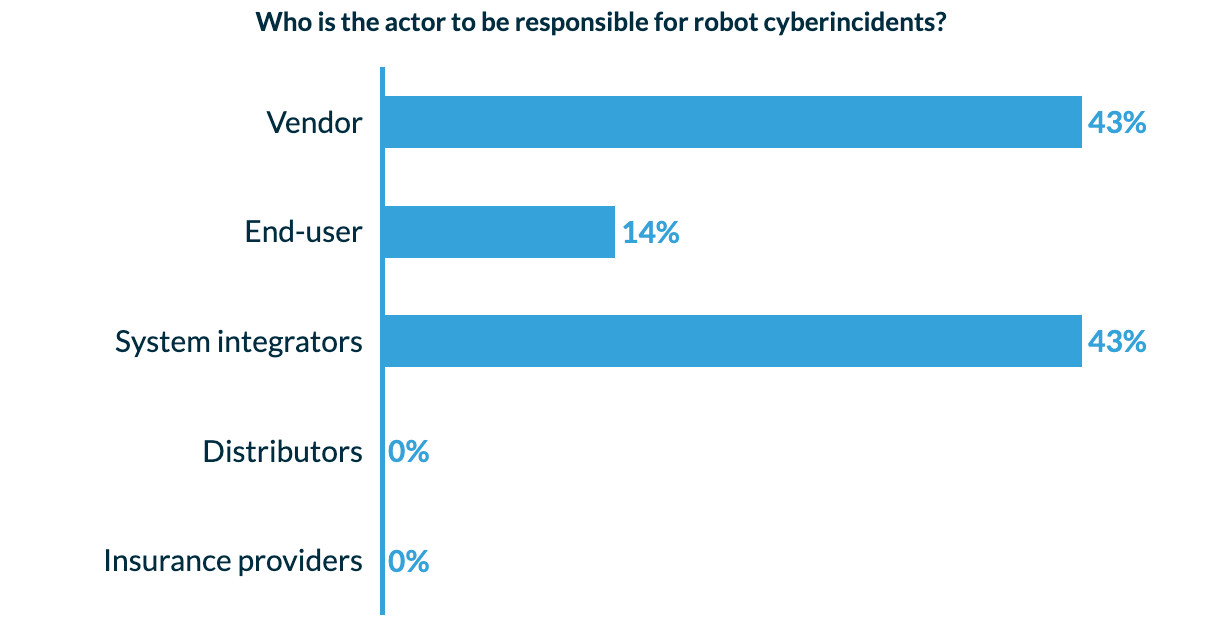
Responsibility is spread across the robotics value chain
To the question of whose responsibility are robot cyberincidents, experts and audience, both considered that it is a responsibility to be shared across the value chain. However, emphasis is put at the manufacturer and system integration side, but also end users (14%) are responsible for secure robot deployments.
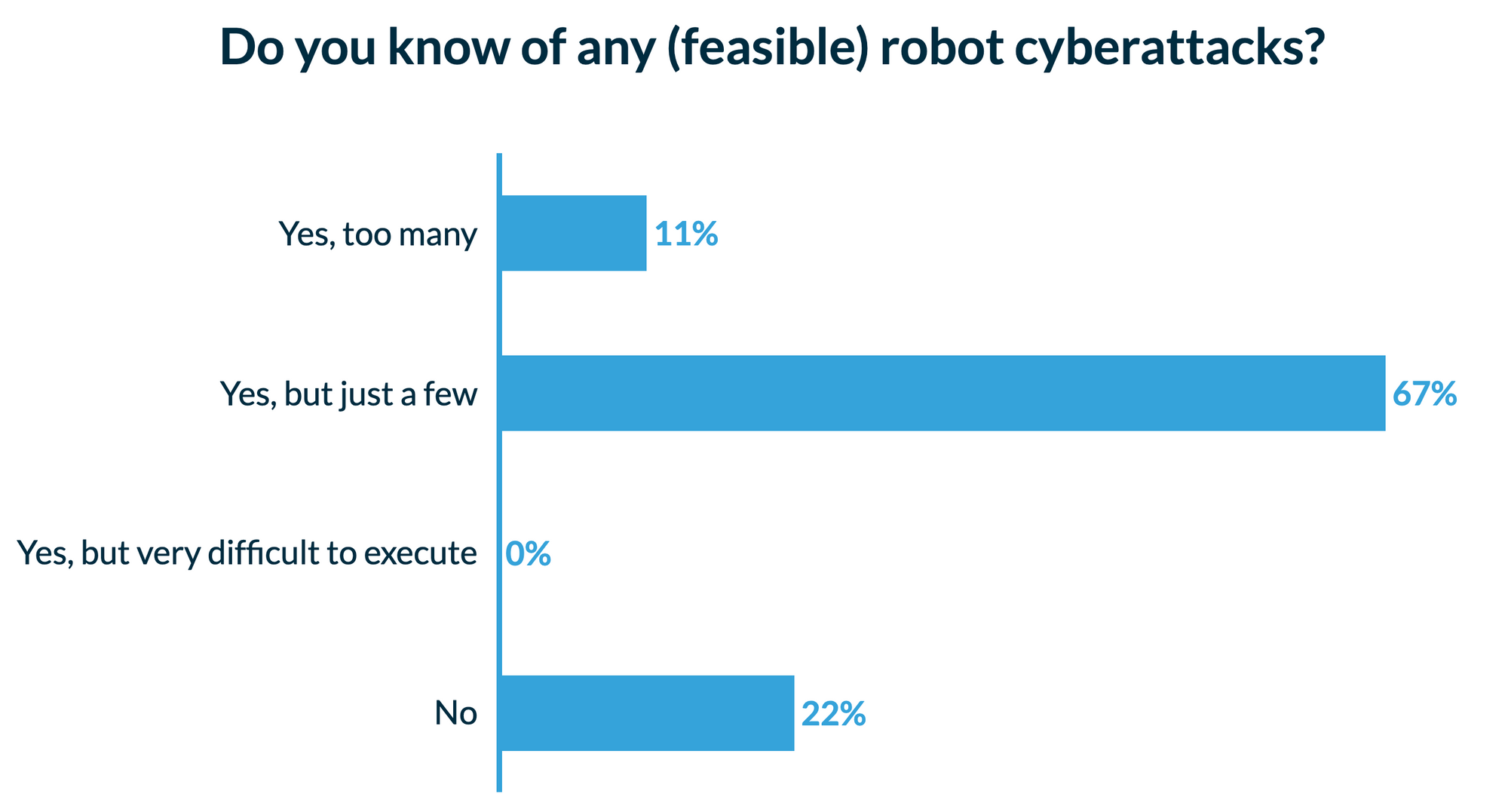
Feasible cyberattacks
If they were to be on the foot of an attacker, most of the audience has identified feasible cyberattacks.
Security standardization in robotics is requested
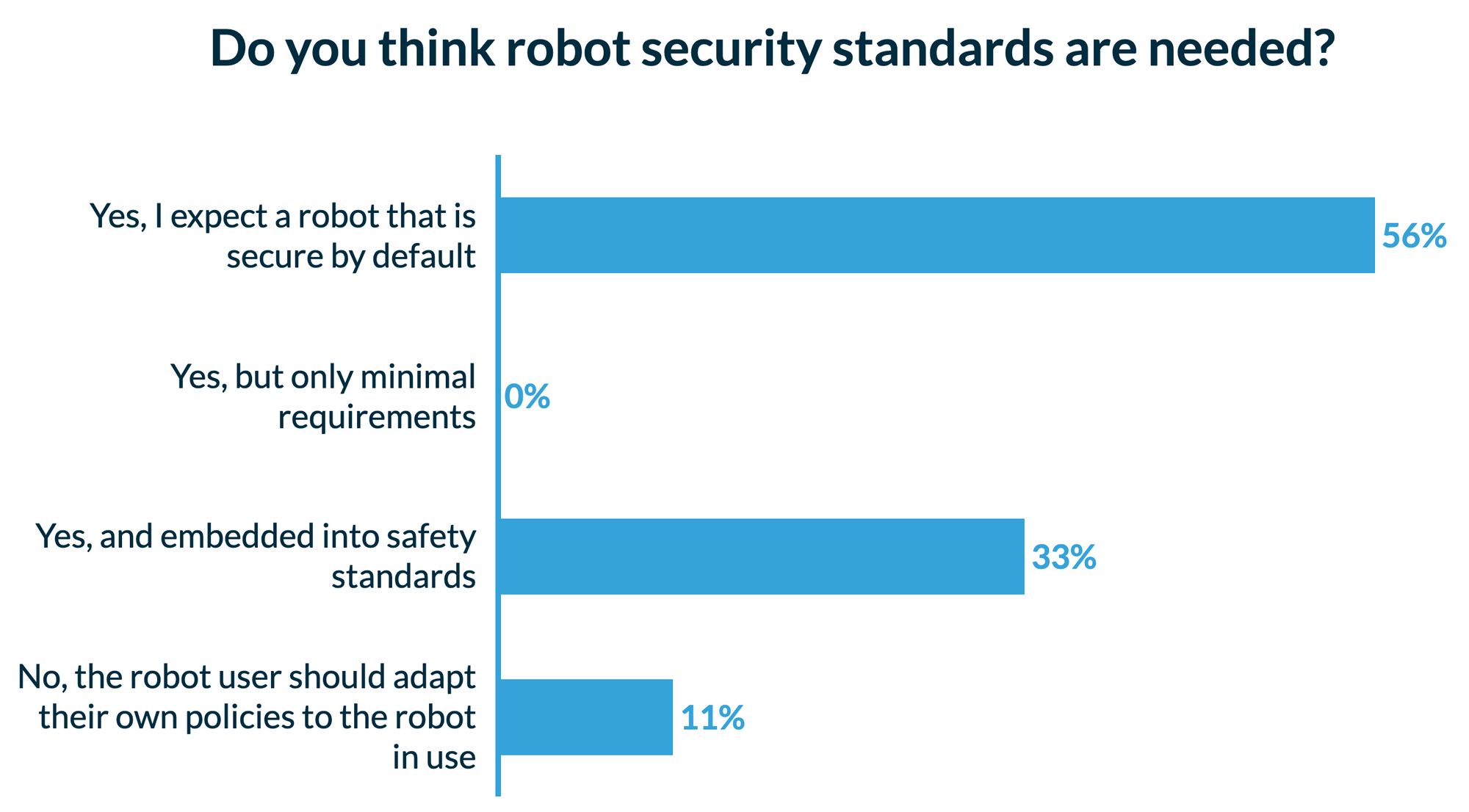 Actions are to be taken when it comes to standardization, as to asure some degree of compliance, according to the panel and the audience. Most of the audience agreed to expect a secure by default robot, but other voices requested security embedded into safety standards.
Actions are to be taken when it comes to standardization, as to asure some degree of compliance, according to the panel and the audience. Most of the audience agreed to expect a secure by default robot, but other voices requested security embedded into safety standards.
RIS, the Robot Immune System
Alias also presented an update on their Robot Immune System, an Endpoint Protection Platform (EPP) system for robots inspired by the biological immune machinery, which now offers supports for leading collaborative robot solutions as well as ROS and ROS2 systems.
Workshops walkthrough
Part I - talk 1: Current security threat landscape in robotics
In this talk, Víctor Mayoral Vilches from Alias Robotics provided an overview of the current cybersecurity threat landscape in robotics by following an offensive approach. Víctor shared state-of-the-art tools for robot cybersecurity research and how his team is pentesting robots and robotic systems around the world while helping companies deliver more cyber-secure solutions.

He wrapped up his speech showing some real examples of vulnerabilities in industrial robots and called for EU robotics community to take an active role supporting the robot cybersecurity growing ecosystem.
Part I - Talk 2: Detection anomalies in CPS environments: Results from the IoT4CPS project
Arndt Bonitz from Austrian Institute of Technology (AIT) shared some ongoing work about the EU funded IoT4CPS project and showed how their technology works in IoT devices by learning from log data. He argued that their work could easily be brought to a variety of robotic applications and showed an interesting demonstrator.

Part I - Talk 3: Robotics honeypots: Learning from robot hackers
Dr. Francisco J. Rodríguez Lera from Universidad de León gave a speech on robot honeypots. He shared that honeypots are typically cyber-deception platforms used to obfuscate the attackers. He showed preliminary results obtained from their honeypot instances and some future work planned to learn more about robot hackers and their behaviour through a robotics deception platform. As of now, misuse dominates the behaviour a varied of attackers that try to take over robot control from all over the world.

Part I - Talk 4: Robot cybersecurity survey
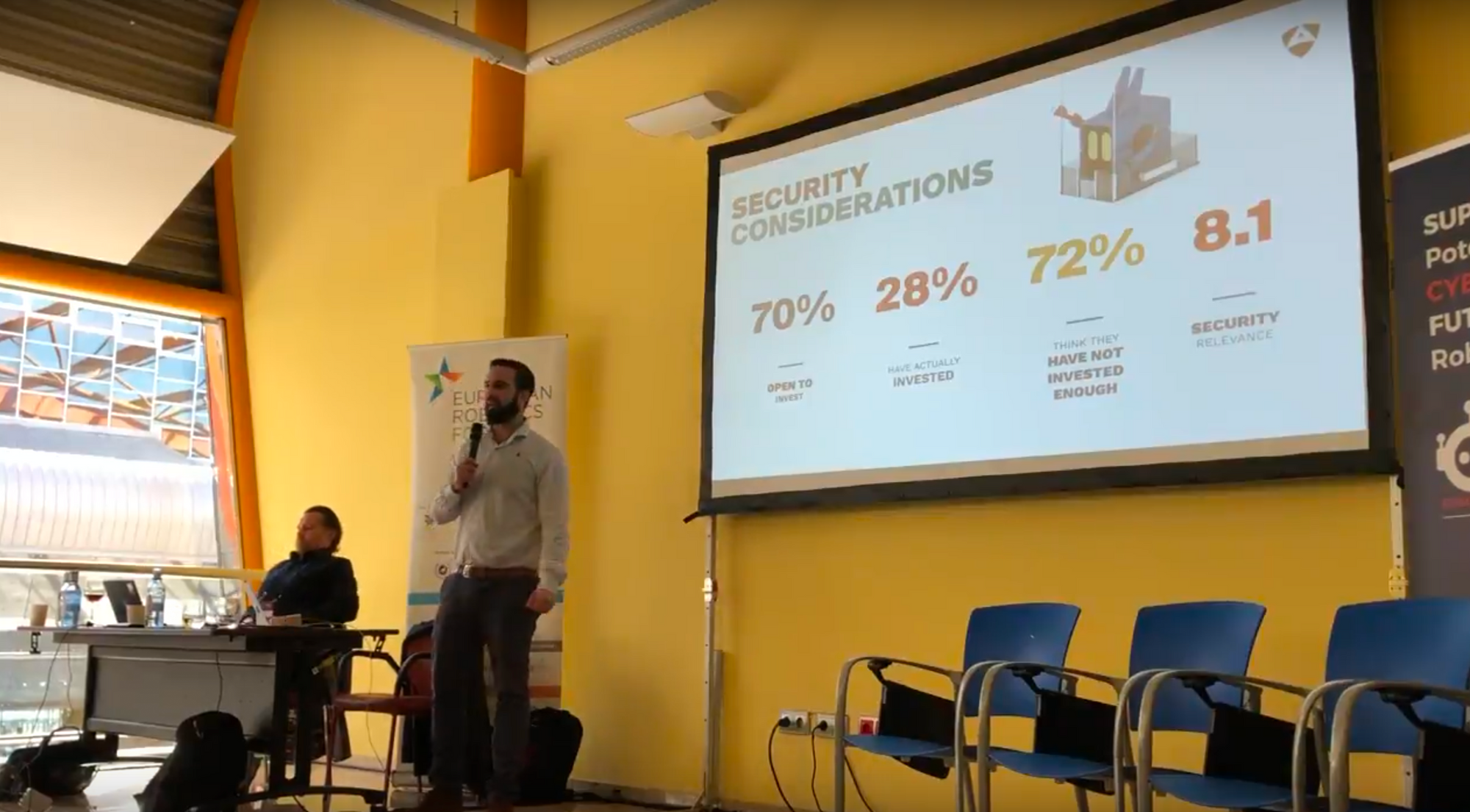
A last minute change in the agenda, Endika Gil Uriarte from Alias Robotics presented results from the robot cybersecurity survey. Endika highlighted that according to available data much work needs to be done in robot cybersecurity:
70% of the robotics companies are open to invest in cybersecurity however only 28% have done so. He pointed at some interesting data gathered and some gaps that need to be further clarified. Finally, he called for participation to the poll at it's final weeks. We need the whole robotics value chain to contribute raising awareness and kindly ask the EU community for support to this initiative.
Part I - Round table: Robot cybersecurity round table, the robotics value chain
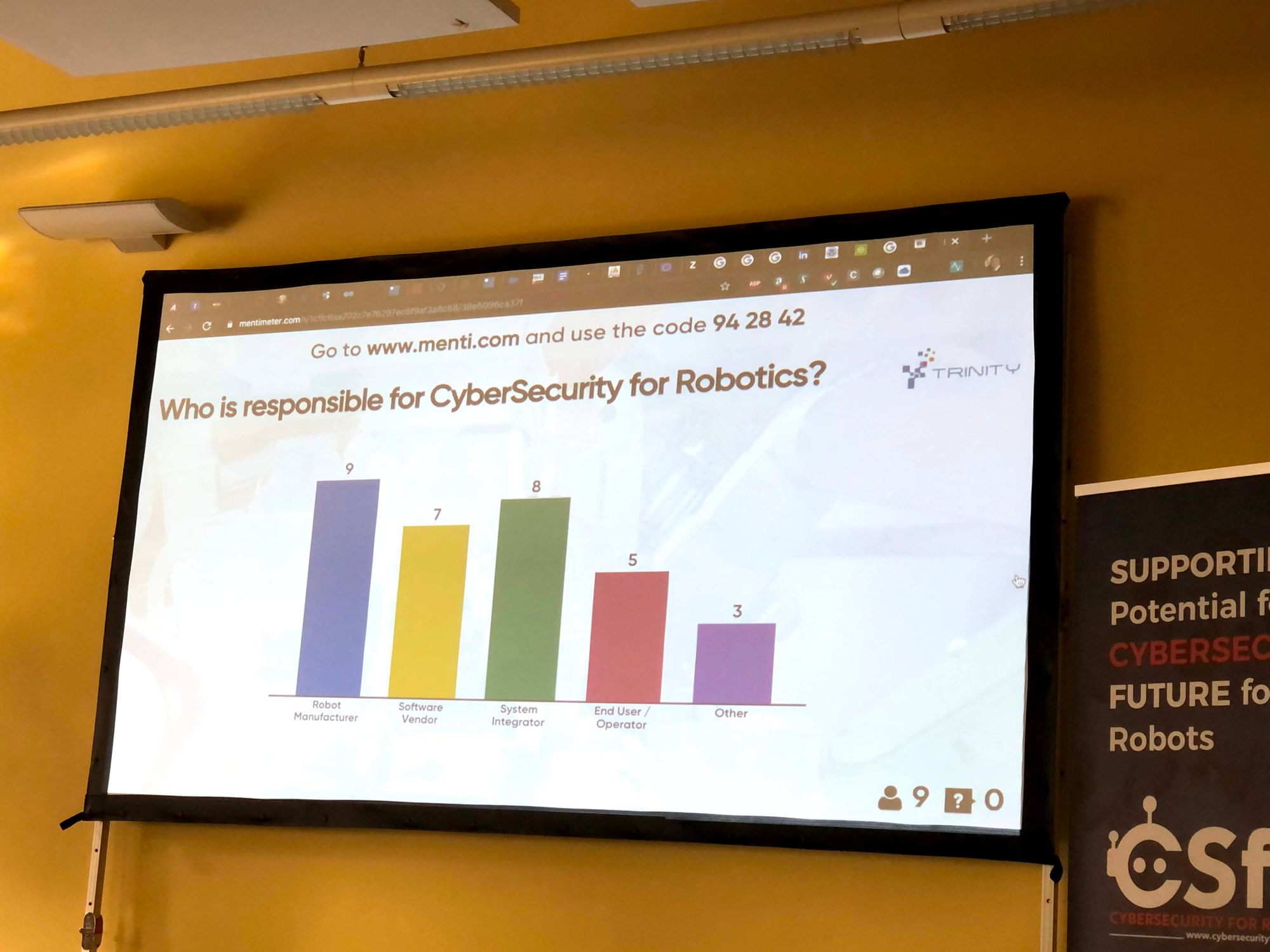
Endika Gil Uriarte from Alias Robotics led a round table that included researchers, security practicioners, robotic system integrators as well as manufacturers. A pretty interested and live discussion on the robotics value chain where the audience could participate actively via an interactive series of questions.

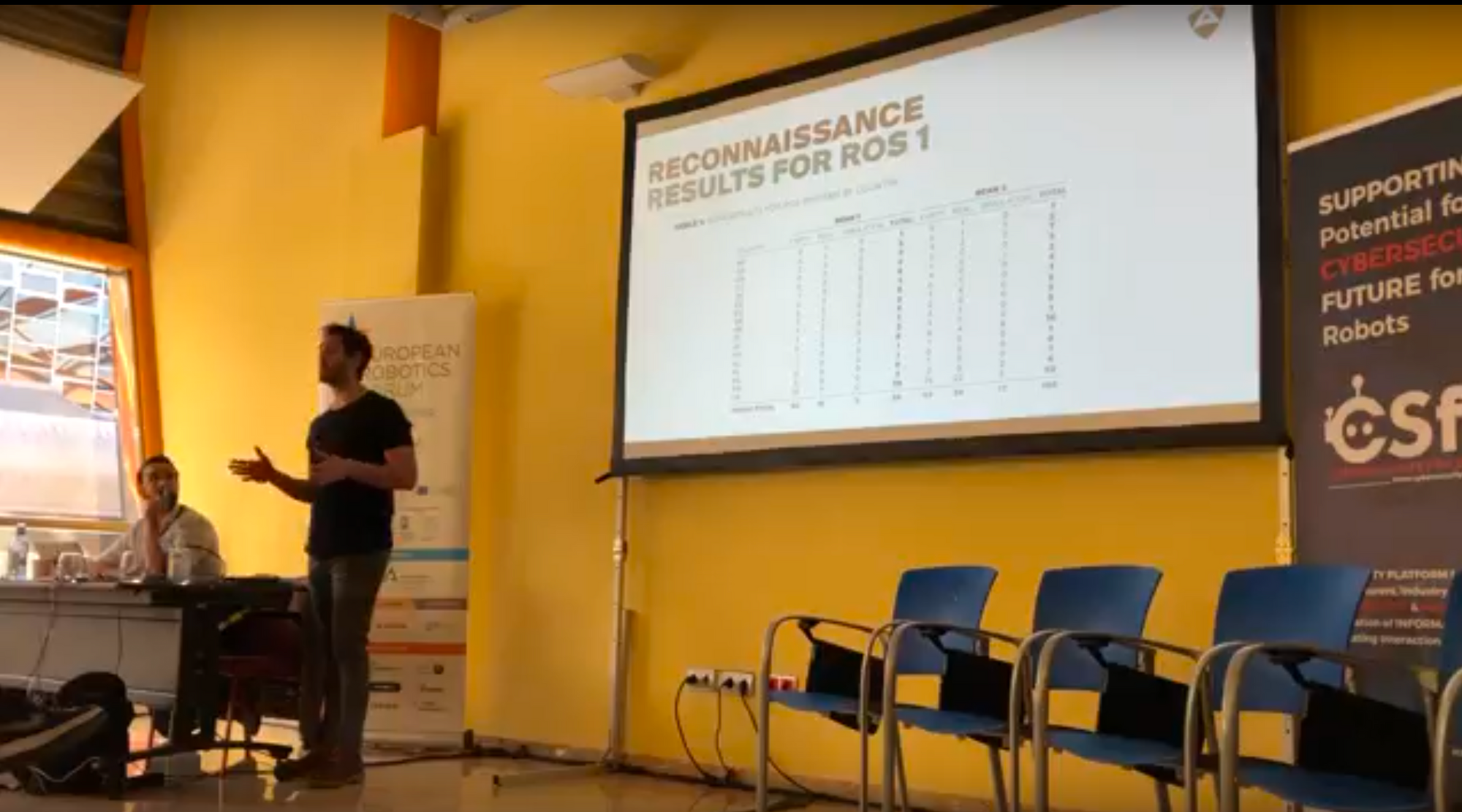
Part II - Talk 1: Security in ROS & ROS 2 robot setups
Víctor Mayoral Vilches from Alias Robotics shared some of the latest developments in securing ROS and ROS2. He summarized current status and where efforts are being placed. He further introduced slightly the importance of securing both communications (communications security) and systems (systems security) while introducing briefly some of his recent work researching how Zero Trust network architectures can be implemented in robotics via Robot Immune System ( RIS).
Part II - Talk 2: Access control Models with application to robotics
Dr. Stefan Rass from Alpen Andria University, an expert in security, gave a master talk where he presented difference access control models and their applications in the robotics domain.
Stefan, who has for decades been an active member of crypto and game theoretic research, discussed why access control is critical in robotics. He leveraged on a comparative overview of the different methods in use, such as discretionary, mandatory, role-based and more models like Bell-LaPadula.
Part II - Talk 3: Researchers, Manufacturers, Integrators, Security Technology providers, End Users and Operators
Unfortunately agenda changed slightly for the second part due to travel problems. Instead of what was planned, Ulrich Seldeslachts from LSEC-TRINITY elaborated on shared roles & responsibilities, risk based approach (what to put in an RFP?) Industry Value chain definition. He argued about raising the awareness of cybersecurity in robotics, and provided some conclusions on CSFR19 which happened Bilbao Cybersecurity. The talk finished with an open debate and Q&A with attendees.

We are currently processing the material presented and the recordings. As soon as we're ready we'll share them and announce here. Stay tuned!

