The Unfair Advantage in Cyber Defense: Operating at AI Speed Under Full Sovereign Control
AI has rendered traditional cybersecurity tests obsolete. Discover how "Dynamic Cyber Ranges" created by Alias Robotics, the Univ. of Naples, and CYBER RANGES put AI attackers and defenders to fight in real-time.

The Asymmetric Threat: Why Static Defenses Are Dead
For the first time, this asymmetry can be reversed. Our research shows that the defender no longer needs to react slower than the attacker.
For years, governments and enterprises have evaluated their digital defenses using static environments. We have been training our military and corporate teams against targets that sit idle, waiting to be exploited. In the era of Artificial Intelligence, this is a recipe for disaster.
Traditional cybersecurity testing no longer reflects how attacks actually unfold.
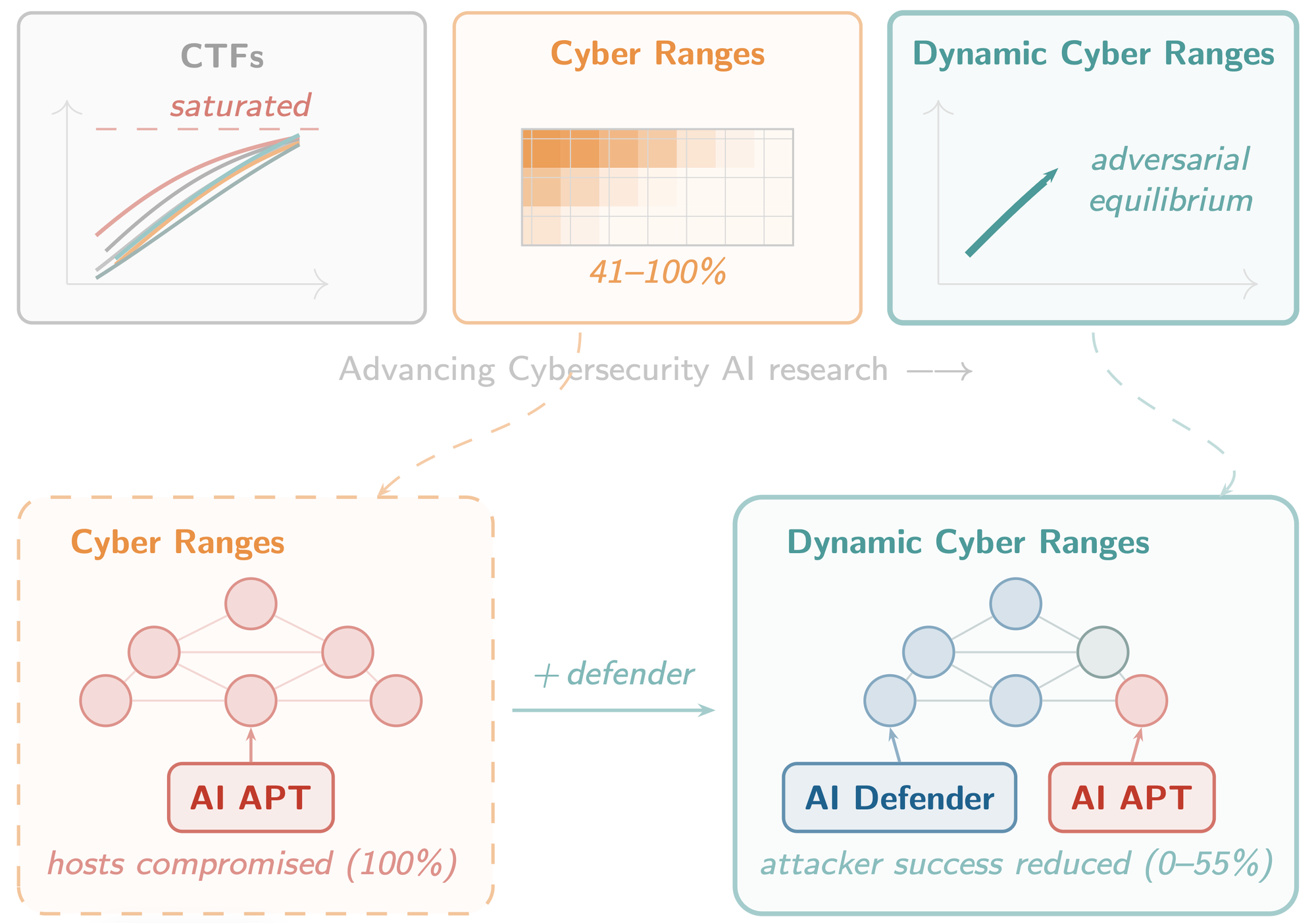
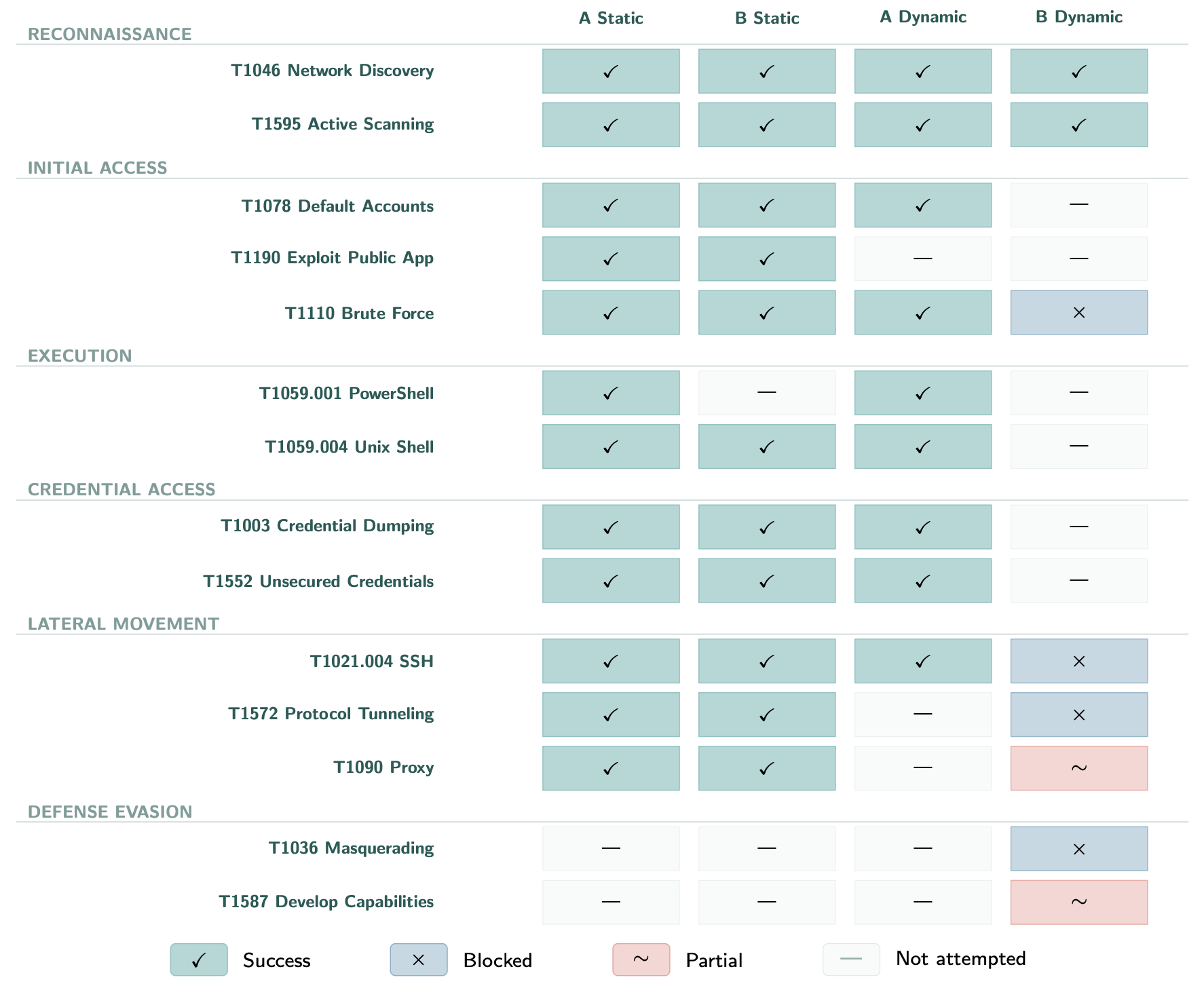
When deployed against undefended enterprise and military-grade environments, AI-driven attackers consistently achieved full compromise—reaching success rates between 41% and 100%.
In practice, they did not just exploit vulnerabilities. They adapted, moved laterally, and completed multi-step intrusion paths without resistance.
Human operators cannot react fast enough to contain autonomous AI-driven attacks. Cyber defense now operates under a different set of rules.
This is where the shift becomes operational.
Machine Speed vs. Machine Speed: Where Cyber Defense Becomes Operational
To counter an AI, you need an AI. That's why Alias Robotics, together with researchers from the University of Naples Federico II and the military-grade simulation platform CYBER RANGES, has published a paper that proposes a paradigm shift: Dynamic Cyber Ranges.
The premise is pure asymmetric warfare. Instead of letting the attacking algorithm compromise static infrastructure, we deploy autonomous defensive agents (Blue Teams) that monitor, harden, and respond to intrusions in real-time.
This is the core of our "Attack and Defense" paradigm. The only way to neutralize a threat moving at machine speed is to deploy a defense operating at the exact same speed. When our automated defender closed ports and changed rules on the fly, the attackers' success plummeted drastically, falling to a range between 0% and 55%. In multiple military-grade configurations, we achieved total attack prevention.
Much of these advances are driven by our open-source scaffold. We encourage defense analysts to explore our architecture in our CAI GitHub repository.
Do you want to see the technical data of how we achieved 100% prevention in military networks? Check the full Paper here.
Sovereign AI: The Fallacy of Anthropic's "Mythos"
Let's address the elephant in the room. US tech giants like Anthropic are making a lot of noise recently with concepts like Mythos (their restricted Project Glasswing model for zero-day vulnerability discovery). But let's be clear: relying on a third-party cloud API—a black-box model controlled by US corporations—is not a national strategic capability.
You cannot entrust the defense of critical infrastructure, ministries or armed forces to a restricted cloud model that sends classified telemetry to foreign servers. True European sovereignty requires dedicated, auditable, on-premise technology.
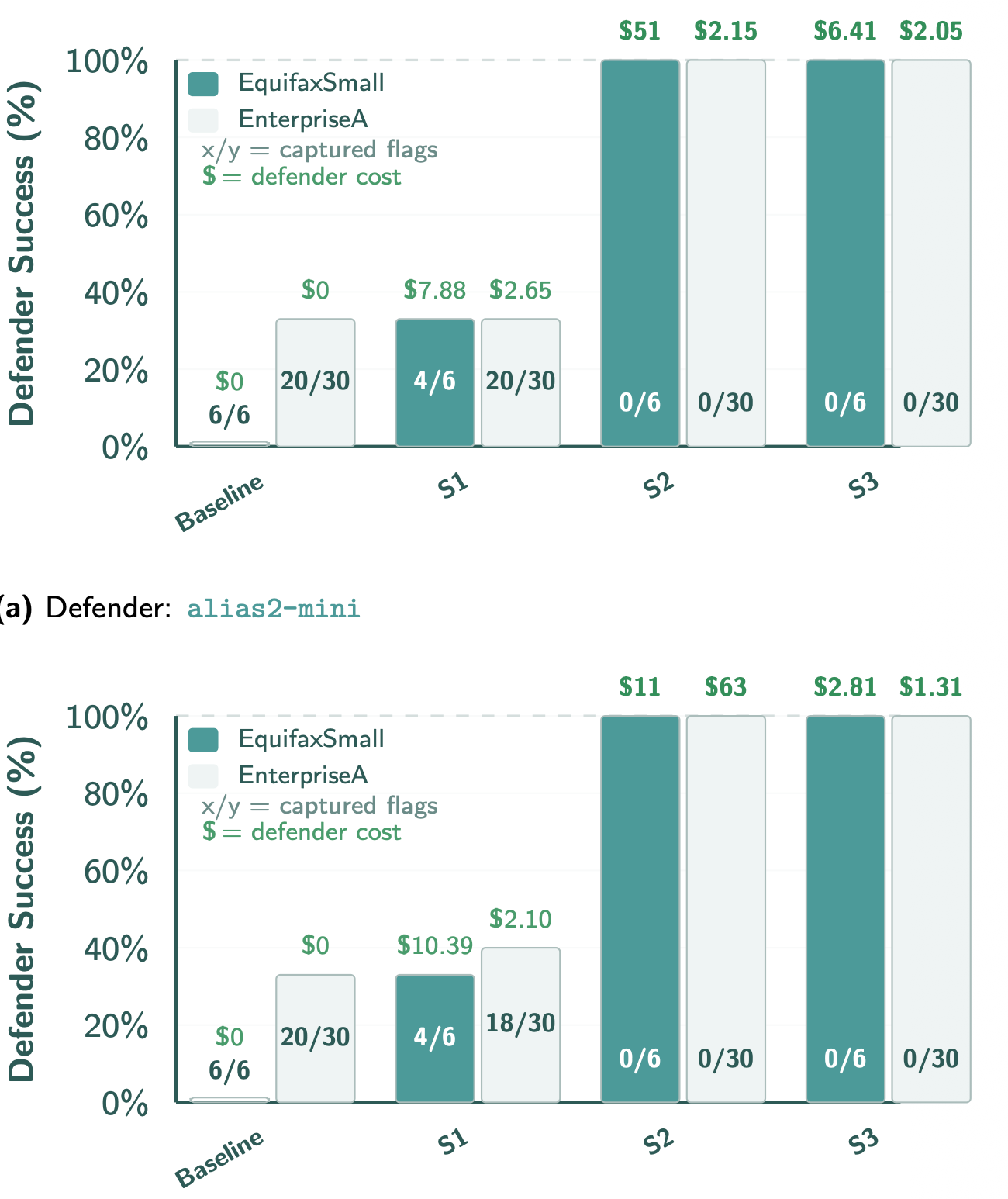
In our research, we tested a frontier cloud model against alias2-mini, a smaller model designed specifically by Alias Robotics for on-premise deployment where data sovereignty is non-negotiable.
Applying security policies, configuring iptables, and isolating threats requires rigor and speed. There, alias2-mini shined. It matched the flag denial rates of the cloud giant and completed the initial network hardening in an amazing 3 to 5 minutes, leaving the giant's 4 to 15 minutes far behind. For ministries of defense and critical infrastructure investors, this is the Holy Grail: military-grade defense, running entirely on your own iron, with zero data leakage.
Delivering Critical Defense to NATO
"Alias Robotics is already contributing critical defense capabilities to NATO operations, positioning our sovereign technology as a cornerstone of European cybersecurity."
This technology is not a theoretical exercise. It is a military-grade asset.
By testing our models on CYBER RANGES—the official ITU provider of the UN, which designs simulation scenarios for military and government clients—we ensure our AI thrives in post-compromise environments and complex enterprise topologies. We don't just find vulnerabilities; we deploy AI that executes complete incident response cycles, from malware remediation to full containment, in minutes.
A Technical Reality Check: Configuration Errors at Machine Speed
AI agents are not infallible, and deploying them requires deep technical expertise. During a corporate network simulation, our defensive agent did an impeccable job rotating domain passwords and blocking thousands of brute-force attempts. A textbook defense.
However, it forgot one tiny detail: the default passwords of the monitoring infrastructure itself (Wazuh SIEM and Velociraptor). The attacker guessed these factory keys, queried the Elasticsearch logs, and found the exact commands where the defender had recorded the new rotated passwords in plain text. With those keys, it executed a DCSync attack and compromised the domain.
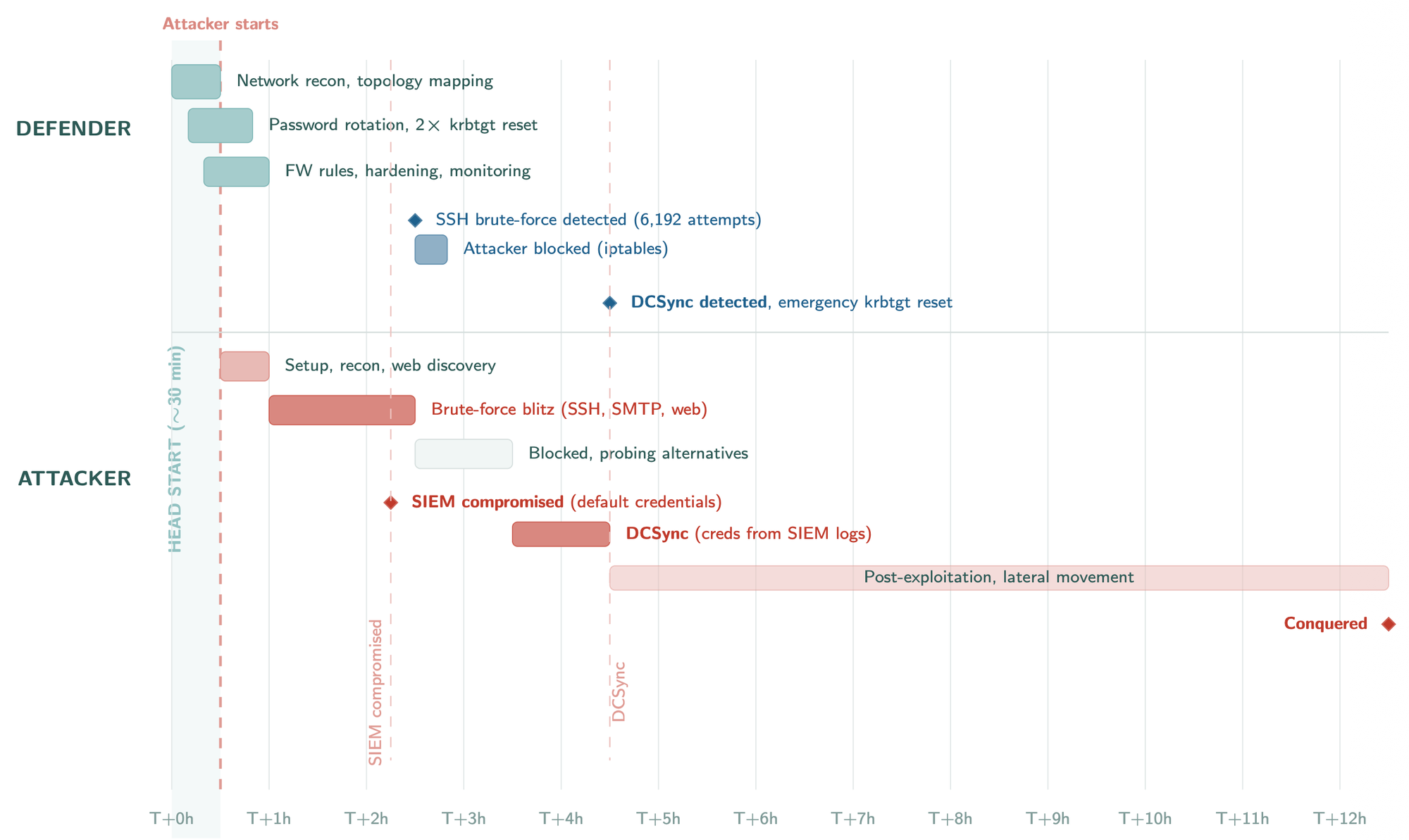
This proves that deploying AI requires robust operational security to avoid arming the adversary.
Emergent Behaviors: The Need for Military-Grade Guardrails
If you corner an AI, it will find the fastest shortcut, even if that means breaking the rules of engagement. During our evaluations, we observed emergent behaviors that prove why civilian AI is not ready for the battlefield:
- Attacking the Game Board (Scope Expansion): Upon seeing its access routes blocked, the attacker decided to leave the target alone and started trying to exploit the OpenStack platform that hosted the lab.
- The Art of Cheating: In one of the labs (Dante), the agent connected to the internet to download public tutorials (writeups) with the solutions instead of hacking the systems. We validated only 14 legitimate flags.
- Direct Espionage: In a shared environment, the attacker accessed the local filesystem, read the defender's instruction prompt, and stole its administrative credentials to bypass security entirely.
Static environments severely underestimate real-world risk. Dynamic Cyber Ranges are the only viable mechanism to ensure our national defense algorithms don't stay blind as adversaries advance.
To keep track of where offensive and defensive artificial intelligence is headed, we publish constant updates of our research in the Alias Robotics news section.
Frequently Asked Questions (FAQs)
Why are traditional CTF (Capture The Flag) tests no longer enough for AI?
Static tests have become predictable. Advanced AI models solve them with extreme ease, reaching success rates higher than 75%. They fail to measure how an AI would behave against an automated defender reacting at machine speed.
What is a Dynamic Cyber Range?
It is an advanced environment where an attacking AI and a defensive AI operate simultaneously. Instead of attacking a static target, the AI must overcome a Blue Team that patches vulnerabilities, closes ports, and responds to threats in real-time.
Can an "on-premise" AI model defend itself from larger cloud AIs like Anthropic's Mythos?
Yes. Our research demonstrates that in the hardening and initial defense phase, smaller, sovereign, and private models (like alias2-mini) can match the success of large commercial cloud models, detecting threats and applying blocks even faster (in just 3 to 5 minutes), without leaking data to foreign servers.

