Military-Grade Sovereign AI: Securing National Strategic Capability at Locked Shields by CCDCOE
Alias Robotics proves at Locked Shields why modern cyber defense demands military-grade, on-premise AI. Discover the end of static security.

5 min read
Any national security strategist knows it well: the rules of engagement have completely shifted. While state-sponsored attackers are already deploying offensives at the speed dictated by artificial intelligence, a massive chunk of the industry still relies on disconnected, reactive tools. However, the recent edition of Locked Shields 2026—the world's largest and most complex live-fire cyber defense exercise organized by NATO CCDCOE— has marked an irreversible turning point.
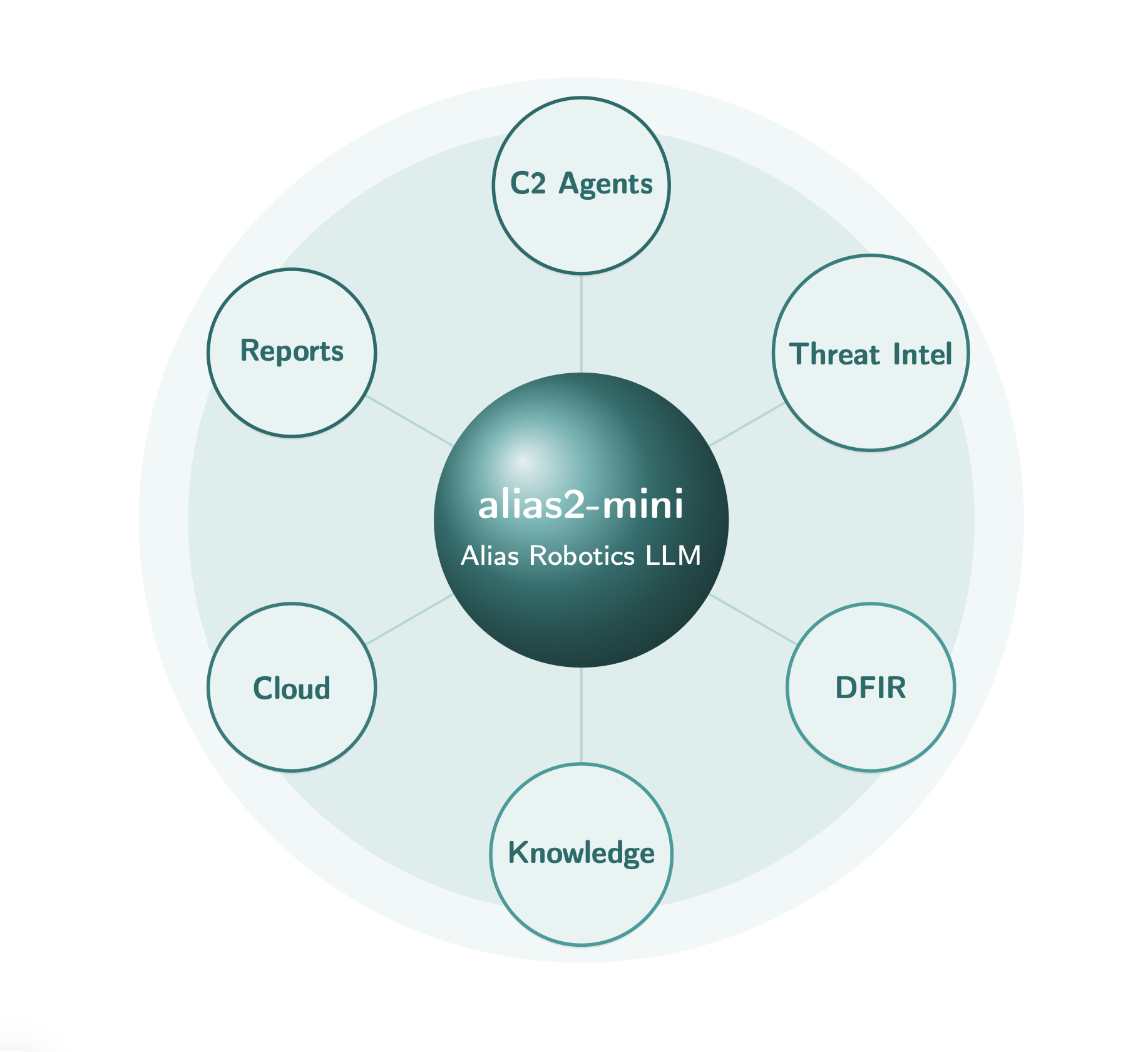
There, the Alias Robotics team didn't just test another monitoring software. We demonstrated how our proprietary large language models (LLMs) and Cybersecurity AI (CAI) can operate semi-autonomous defense systems under heavy crossfire. It has become glaringly obvious that our technology transcends the "tool" category to establish itself as a true military-grade, national strategic capability.

The Trap of Static Defense in Dynamic Environments
Continuing to evaluate networks with static audits to stop dynamic threats is, operationally speaking, totally unsustainable. The development of new defense capabilities is no longer centered on standalone tools, but on systems able to operate continuously, at scale, and under human control.
Through our extensive experience in dynamic Attack and Defense environments and military simulators like Cyber Ranges, we've confirmed that the only viable defense is one that strikes back in real-time. As Endika Gil-Uriarte, CEO of Alias Robotics, points out:
"If cyber attackers are using AI, defenders must operate at machine speed. We are seeing cyber defense evolve into systems where sovereign AI becomes a central part of the operational mechanism itself".
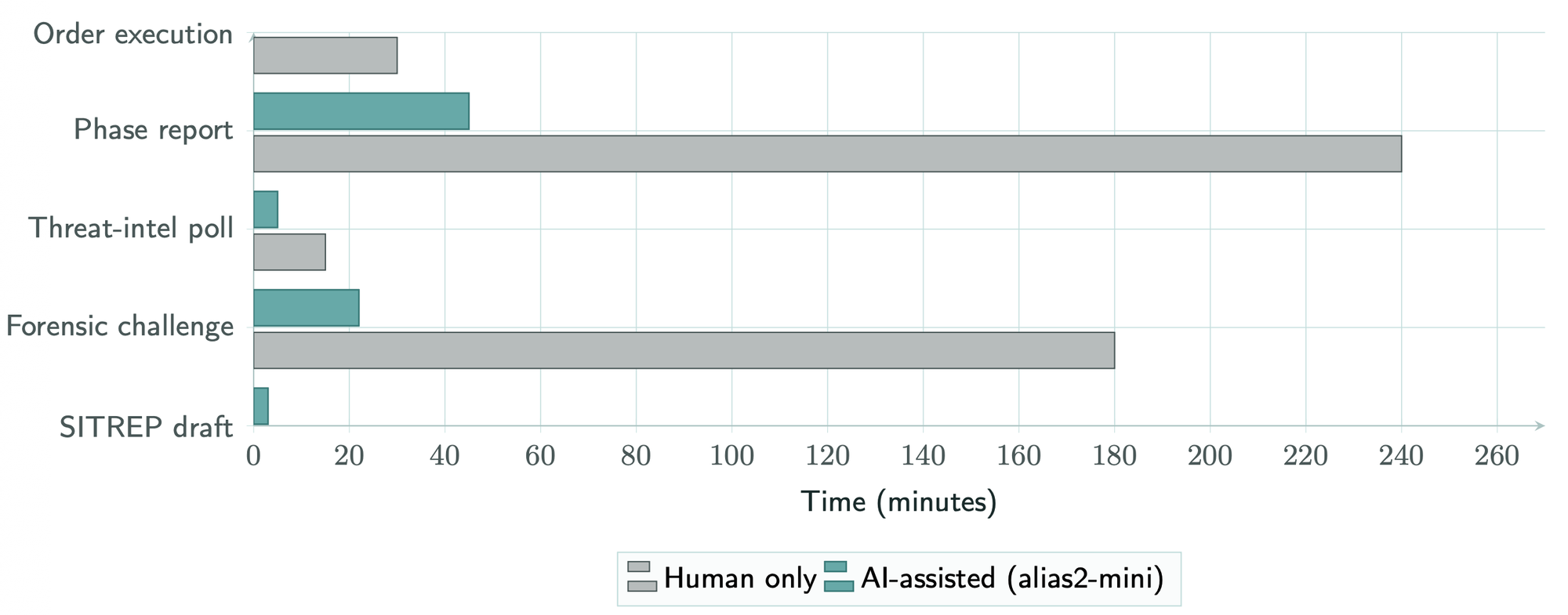
At Locked Shields, our AI proved exactly this by ruthlessly compressing the OODA loop. It radically slashed analysis times, achieving an acceleration of 5 to 10 times compared to human execution. Complex digital forensics challenges that typically consume a senior analyst for 2 to 4 hours were resolved by alias2-mini in just 15 to 30 minutes.
Beyond the "Prompt": Intelligence That Operates, Not Just Assists
Right now, there's a lot of media noise surrounding AI "assistants" that require constant prompting. In the absolute chaos of an attack on critical infrastructure, that approach simply fails. Our Cybersecurity AI (CAI) is an architecture designed to transform defense into a continuous operational capability.

During the exercise, our sovereign LLM processed a staggering 3.5 billion tokens and supported over 60 analysts concurrently with near-zero latency. In one of the most critical scenarios at Locked Shields, this capacity allowed for the recovery of a fully compromised cloud environment in just 14 minutes. Crucially, for institutional peace of mind, all of these actions are executed always under human oversight.
Sovereignty or Nothing: The Illusion of the Commercial Cloud
We see US tech giants grabbing headlines every day with generic models like Mythos. But let's be rigorous: relying on an external commercial cloud API to protect government or military networks does not grant you a national capability.
One of the central requirements in modern defense programs is ensuring that capabilities can be deployed without compromising data sovereignty or infrastructure control. During the NATO exercise, our technology operated 100% on-premise, entirely within the team's perimeter. Recent national cybersecurity strategies, make it crystal clear: the institutional goal isn't buying cloud licenses; the goal is to secure a national capability.
The Roadmap Towards Sovereign National Capabilities
The shift we are witnessing is structural. Our clear roadmap for defense customers focuses on the integration into existing defense architectures and scalability across national operations.
We are working side by side with Ministries of Defense, Public administration, and critical infrastructure providers to augment their defensive operations at the speed of AI. If your responsibility is safeguarding your nation's critical assets, it's time to deploy a battle-tested technology that fights at your exact same speed.
Frequently Asked Questions (FAQs)
- What does "military-grade" really mean in this context? It means the infrastructure doesn't collapse under fire. It provides total autonomy and the capability to survive by operating 100% on-premise, without sending network topology or credentials to external servers.
- Are these AI systems acting entirely on their own? No. Our semi-autonomous defense systems are built to eliminate execution delays while remaining always under human oversight.
- Why is "securing a national capability" so crucial? It means your country is the undisputed owner of its defense. By using proprietary LLMs instead of third-party cloud APIs, you are not vulnerable to external outages or vendor changes. You audit the code, you control the hardware, you defend yourself.
Dive Deeper into Our Technology:
- Meet alias2-mini: The standard for sovereign cybersecurity - Discover how our compact AI model allows organizations to maintain total control of their physical infrastructure.
- CAI PRO: Beyond the human bottleneck - We document the path toward defensive superintelligence and operational scalability.
- European-built AI sets a new global benchmark - Our autonomous model ranked #1 at the NeuroGrid CTF, proving that static defenses are obsolete.
The framework revolutionizing security operations (CAI) - Check out the latest architectural updates to our core CAI framework.


